Schedule VMware Exam
In this post, I will show you step by step how to schedule a VMware exam.
The Process
The entire process is split into a few stages.
- Testing Portal Login
- Private Access Codes
- Exam Selection
- Testing Center
- Voucher and Promo Codes
- Payment
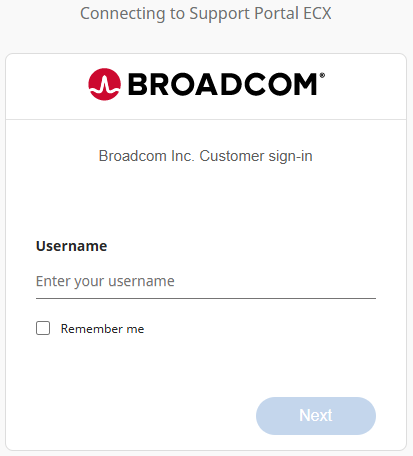
Testing Portal Login
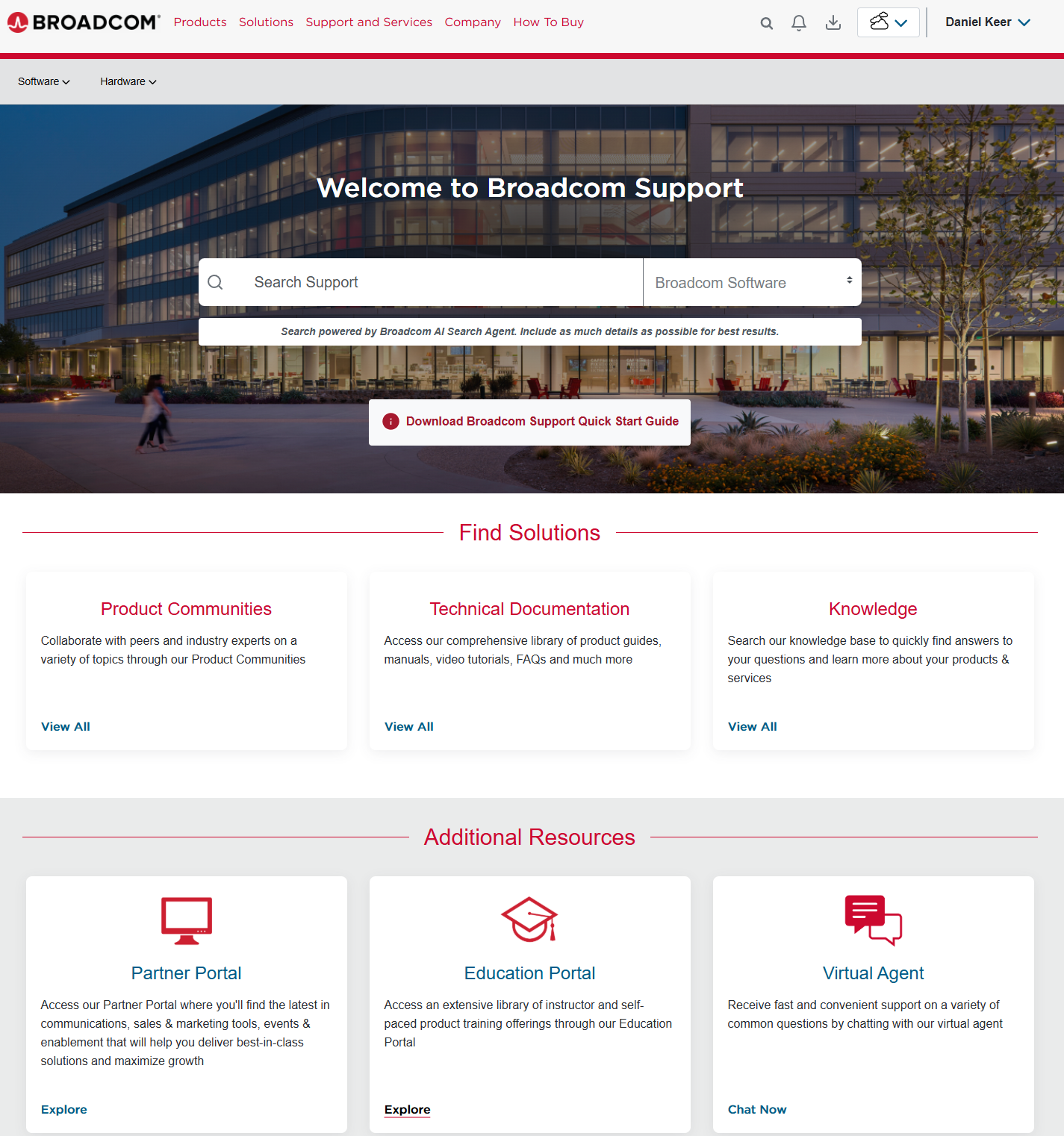
- Log in to the Broadcom Support portal https://support.broadcom.com/
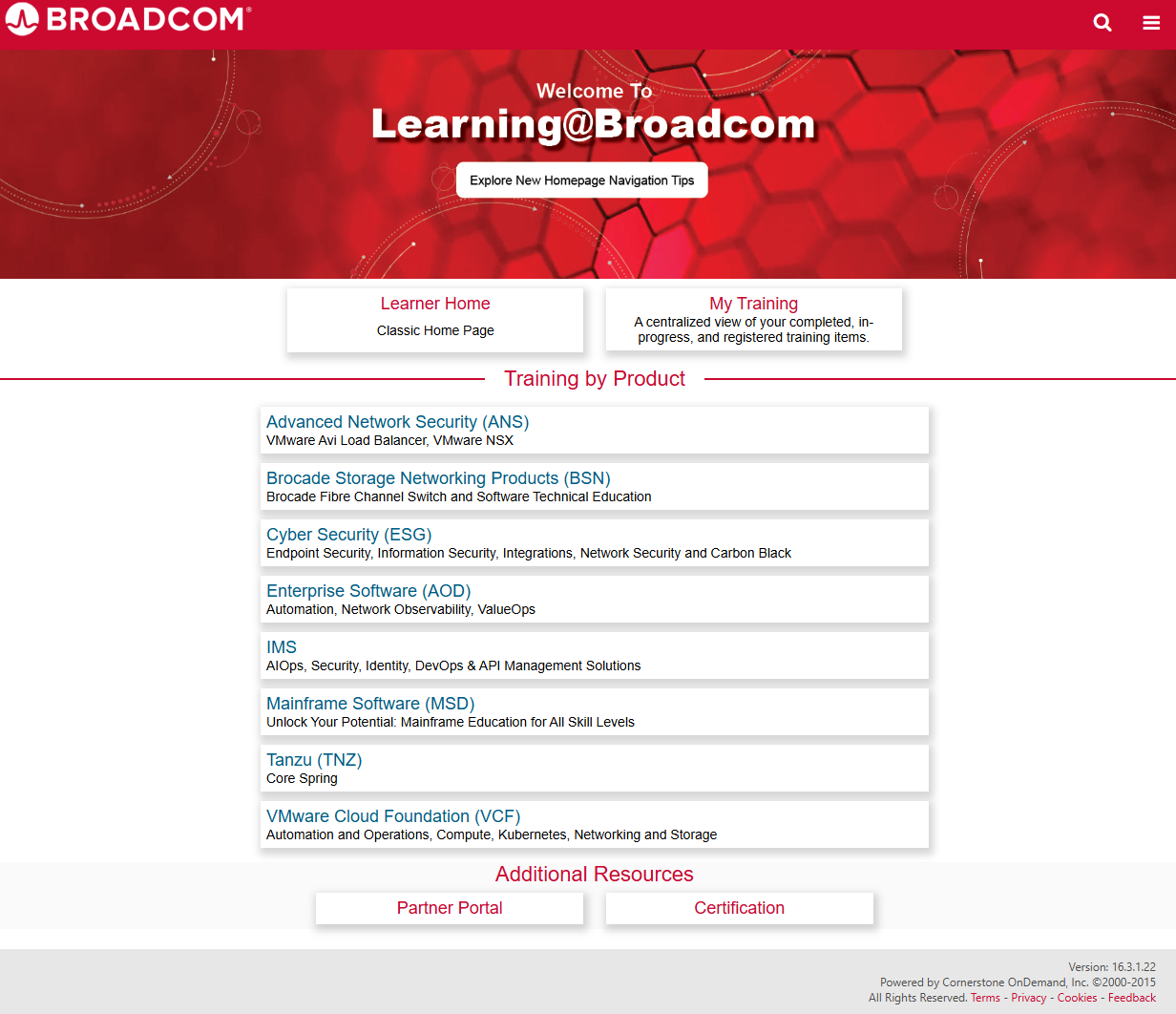
- In the Additional Resources section, on the Education Portal tile, click Explore.
- On the new page that opened up under the Addition Resources section, click on Certification.
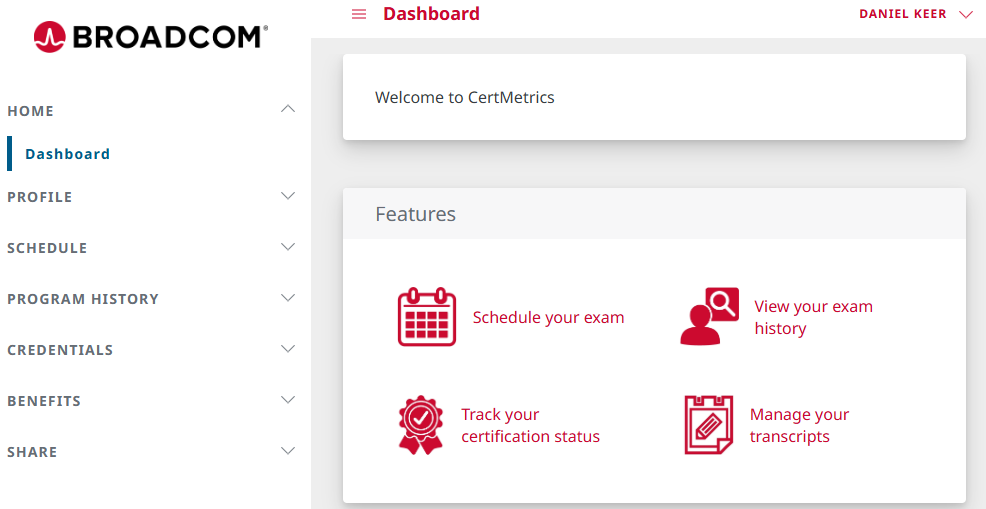
If you want, you can skip those clicks and go directly to the following URL https://cp.certmetrics.com/vmware/en/home/dashboard
- Under Features, click on Schedule your exam.
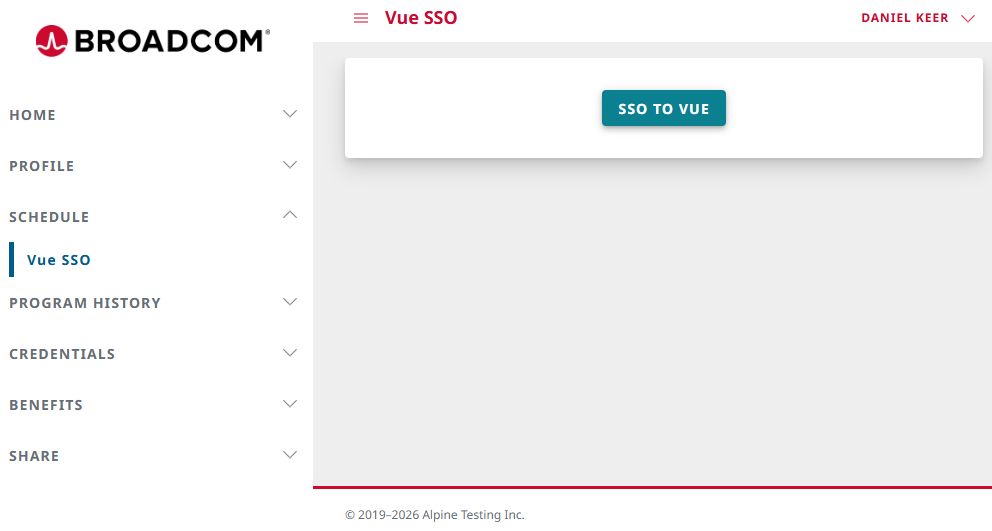
- Click on SSO to Vue.
Private Access Codes
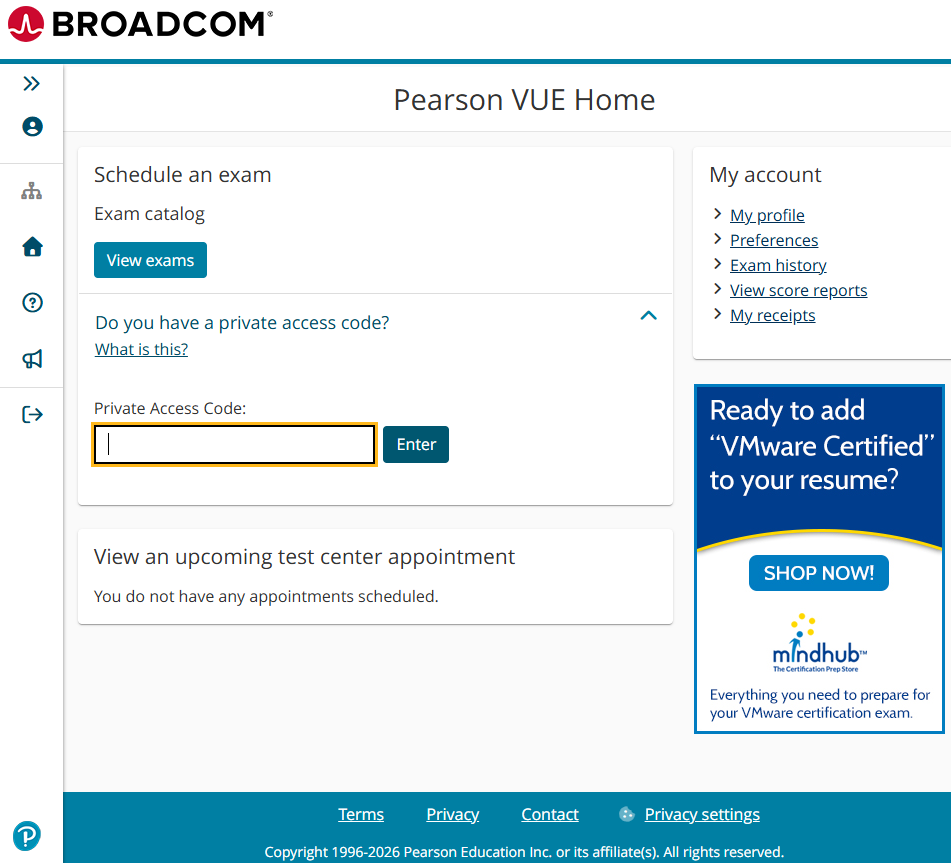
If you are taking a VMware exam at a conference, you will likely have a private access code to access the on-site exam center.
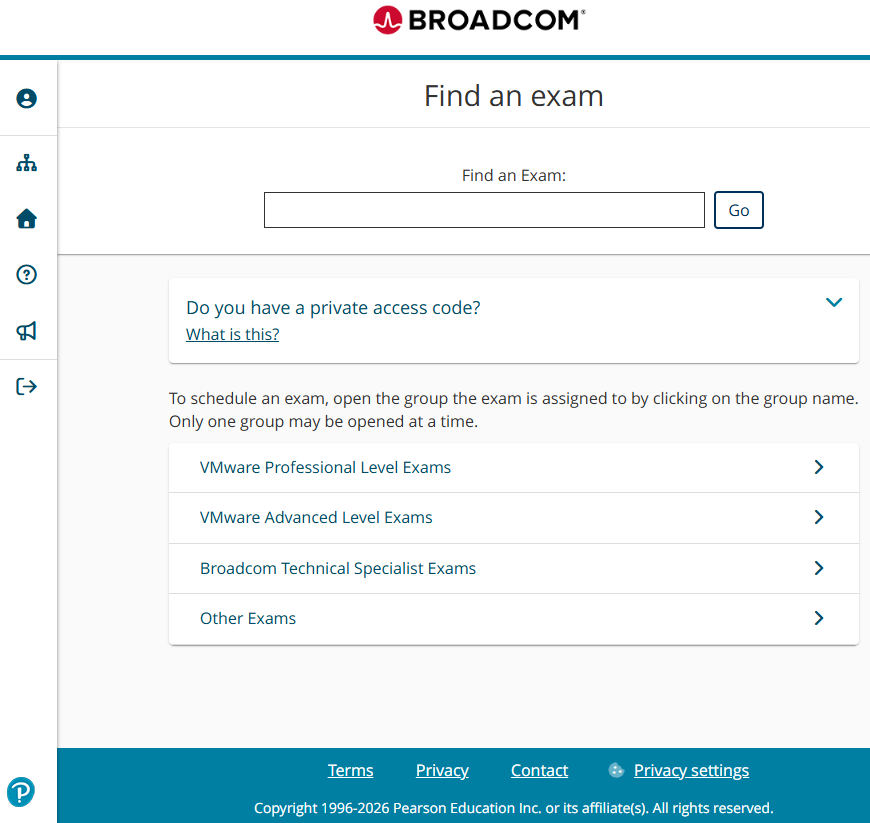
- Click Private Access Code, type in the Private Access Code, then click Enter.
Exam Selection
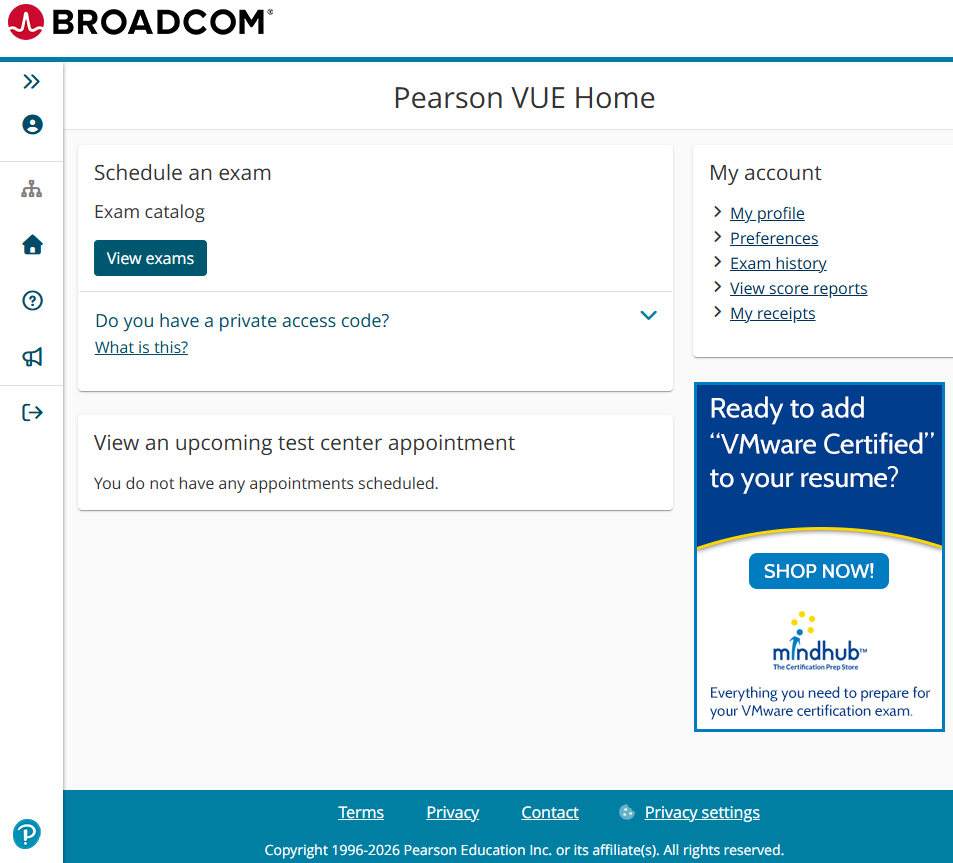
- Click on View exams.
- Depending on the exam you are taking, you may need to click on VMware Professional Level Exams or VMware Advanced Level Exams. You can also search for the exam.